Resultados
Finalizado o scan, o OpenVAS me permite entrar nos detalhes de cada task
Windows XP

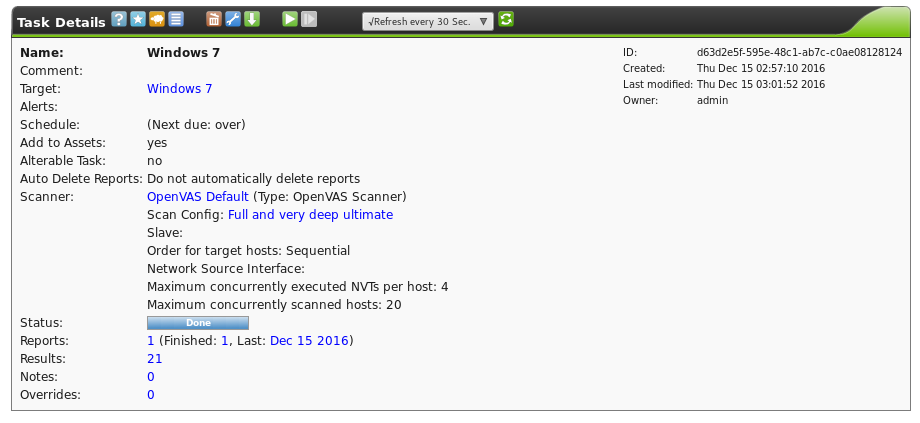
Windows 7
Ubuntu

Em resumo, obtive os seguintes resultados
| Target | Host | High | Medium | Low | Log |
| Windows XP | 192.168.0.12 | 4 | 0 | 0 | 15 |
| Windows 7 | 192.168.0.13 | 0 | 3 | 1 | 17 |
| Ubuntu | 192.168.0.11 | 0 | 0 | 0 | 4 |
| Total | 4 | 4 | 3 | 1 | 36 |
Claramente podemos ver o contraste entre o Windows XP e o Windows 7. Apesar de o Windows 7 ter tido mais respostas, no Windows XP foi possível detectar mais casos de alto nível crítico. Enquanto isso, com o Ubuntu 16.04 obtive apenas 4 resultados e todos foram do tipo Log.
Essa versão do Ubuntu é a mais estável atualmente, torna-se até uma comparação injusta com as outras duas máquinas.
Para o Windows XP, tivemos um alerta de que o sistema operacional está "morto", isso já era algo conhecido nosso. Porém, a terceira vulnerabilidade já é algo mais preocupante, pois uma brecha no SMB permite com que atacantes execute um código na máquina, faça um DoS ou um bypass na autenticação por brute force. Para solucionar, basta fazer as atualizações de segurança.
Para o Windows 7 a preocupação é menor, uma brecha de nível médio permite enumerar os serviços do Ambiente de Computação Distribuida. Para resolver tal problema, é proposto filtrar o tráfego na porta 135.
Logo abaixo, fiz uma exportação de trechos html do resultado do OpenVAS
Resultado por target
Windows XP
| Number of results: | 19 |
Port Summary
| Service (Port) | Threat Level |
| 445/tcp | High |
| general/icmp | Log |
| 137/udp | Log |
| 123/udp | Log |
| 139/tcp | Log |
| general/tcp | High |
| general/CPE-T | Log |
| general/SMBClient | Log |
Security Issues
OS End Of Life Detection
The Operating System on the remote host has reached the end of life and should not be used anymore
The Operating System (cpe:/o:microsoft:windows_xp) on the remote host has reached the end ↵ of life at 08 Apr 2014 and should not be used anymore. See https://support.microsoft.com/de-de/lifecycle/search?sort=PN&qid=&alpha=Microsoft%20Wi↵ ndows%20XP&Filter=FilterNO for more information.
Details: OS End Of Life Detection (OID: 1.3.6.1.4.1.25623.1.0.103674)
Version used: $Revision: 4111 $
This host is missing a critical security update according to Microsoft Bulletin MS09-001.
Vulnerability was detected according to the Vulnerability Detection Method.
Successful exploitation could allow remote unauthenticated attackers to cause denying the service by sending a specially crafted network message to a system running the server service.
Impact Level: System/Network
Solution type: VendorFix
Run Windows Update and update the listed hotfixes or download and update mentioned hotfixes in the advisory from the below link, http://www.microsoft.com/technet/security/bulletin/ms09-001.mspx
Microsoft Windows 2K Service Pack 4 and prior. Microsoft Windows XP Service Pack 3 and prior. Microsoft Windows 2003 Service Pack 2 and prior.
The issue is due to the way Server Message Block (SMB) Protocol software handles specially crafted SMB packets.
Details: Vulnerabilities in SMB Could Allow Remote Code Execution (958687) - Remote (OID: 1.3.6.1.4.1.25623.1.0.900233)
Version used: $Revision: 4692 $
| CVE: | CVE-2008-4114, CVE-2008-4834, CVE-2008-4835 |
| BID: | 31179 |
| Other: | http://www.milw0rm.com/exploits/6463 |
| http://www.microsoft.com/technet/security/bulletin/ms09-001.mspx |
This host is missing a critical security update according to Microsoft Bulletin MS10-012.
Vulnerability was detected according to the Vulnerability Detection Method.
Successful exploitation will allow remote attackers to execute arbitrary code or cause a denial of service or bypass the authentication mechanism via brute force technique. Impact Level: System/Application
Solution type: VendorFix
Run Windows Update and update the listed hotfixes or download and update mentioned hotfixes in the advisory from the below link, http://www.microsoft.com/technet/security/bulletin/ms10-012.mspx
Microsoft Windows 7 Microsoft Windows 2000 Service Pack and prior Microsoft Windows XP Service Pack 3 and prior Microsoft Windows Vista Service Pack 2 and prior Microsoft Windows Server 2003 Service Pack 2 and prior Microsoft Windows Server 2008 Service Pack 2 and prior
- An input validation error exists while processing SMB requests and can be exploited to cause a buffer overflow via a specially crafted SMB packet. - An error exists in the SMB implementation while parsing SMB packets during the Negotiate phase causing memory corruption via a specially crafted SMB packet. - NULL pointer dereference error exists in SMB while verifying the 'share' and 'servername' fields in SMB packets causing denial of service. - A lack of cryptographic entropy when the SMB server generates challenges during SMB NTLM authentication and can be exploited to bypass the authentication mechanism.
Details: Microsoft Windows SMB Server NTLM Multiple Vulnerabilities (971468) (OID: 1.3.6.1.4.1.25623.1.0.902269)
Version used: $Revision: 4161 $
| CVE: | CVE-2010-0020, CVE-2010-0021, CVE-2010-0022, CVE-2010-0231 |
| CERT: | DFN-CERT-2010-0192 |
| Other: | http://secunia.com/advisories/38510/ |
| http://support.microsoft.com/kb/971468 | |
| http://www.vupen.com/english/advisories/2010/0345 | |
| http://www.microsoft.com/technet/security/bulletin/ms10-012.mspx |
This host is running Linux and prone to remote denial of service vulnerability.
Vulnerability was detected according to the Vulnerability Detection Method.
Successful exploitation may allow remote attackers to cause a kernel crash, denying service to legitimate users. Impact Level: System
Upgrade to Linux Kernel version 3.0.17, 3.1.9 or 3.2.1 For updates refer to http://www.kernel.org
Linux Kernels above or equal to 2.6.36
The flaw is due to an error in IGMP protocol implementation, which can be exploited to cause a kernel crash via specially crafted IGMP queries.
Details: Linux Kernel IGMP Remote Denial of Service Vulnerability (OID: 1.3.6.1.4.1.25623.1.0.802295)
Version used: $Revision: 3062 $
| CVE: | CVE-2012-0207 |
| BID: | 51343 |
| CERT: | DFN-CERT-2012-2075 , DFN-CERT-2012-1697 , DFN-CERT-2012-1272 , DFN-CERT-2012-0426 , DFN-CERT-2012-0360 , DFN-CERT-2012-0241 |
| Other: | http://secunia.com/advisories/47472 |
| http://www.exploit-db.com/exploits/18378 | |
| http://www.securitytracker.com/id/1026526 | |
| http://bugs.debian.org/cgi-bin/bugreport.cgi?bug=654876 | |
| http://womble.decadent.org.uk/blog/igmp-denial-of-service-in-linux-cve-2012-0207.html | |
| http://git.kernel.org/?p=linux/kernel/git/torvalds/linux-2.6.git;a=commitdiff;h=a8c1f65c79cbbb2f7da782d4c9d15639a9b94b27 |
The remote host responded to an ICMP timestamp request. The Timestamp Reply is an ICMP message which replies to a Timestamp message. It consists of the originating timestamp sent by the sender of the Timestamp as well as a receive timestamp and a transmit timestamp. This information could theoretically be used to exploit weak time-based random number generators in other services.
Vulnerability was detected according to the Vulnerability Detection Method.
Details: ICMP Timestamp Detection (OID: 1.3.6.1.4.1.25623.1.0.103190)
Version used: $Revision: 3115 $
| CVE: | CVE-1999-0524 |
| CERT: | CB-K15/1514 , CB-K14/0632 , DFN-CERT-2014-0658 |
| Other: | http://www.ietf.org/rfc/rfc0792.txt |
This script consolidates the OS information detected by several NVTs and tries to find the best matching OS.
Best matching OS:
cpe:/o:microsoft:windows_xp
Found by NVT 1.3.6.1.4.1.25623.1.0.102011 (SMB NativeLanMan)
Other OS detections (in order of reliability):
OS: cpe:/o:microsoft:windows_server_2003 found by NVT 1.3.6.1.4.1.25623.1.0.108021 (Nmap O↵
S Identification (NASL wrapper))
OS: cpe:/o:microsoft:windows found by NVT 1.3.6.1.4.1.25623.1.0.102002 (ICMP based OS Fing↵
erprinting)
Details: OS Detection Consolidation (OID: 1.3.6.1.4.1.25623.1.0.105937)
Version used: $Revision: 4259 $
This plugin runs nmap to identify the remote Operating System.
Detected OS: Microsoft Windows XP SP2 or SP3, or Windows Server 2003
CPE: cpe:/o:microsoft:windows_server_2003
Concluded from Nmap TCP/IP fingerprinting :
OS details: Microsoft Windows XP SP2 or SP3, or Windows Server 2003
OS CPE: cpe:/o:microsoft:windows_xp cpe:/o:microsoft:windows_server_2003
Details: Nmap OS Identification (NASL wrapper) (OID: 1.3.6.1.4.1.25623.1.0.108021)
Version used: $Revision: 4662 $
| Other: | https://nmap.org/book/man-os-detection.html |
| https://nmap.org/book/osdetect.html |
This plugin checks if the port scanners did not kill a service.
OpenVAS cannot reach any of the previously open ports of the remote
host at the end of its scan.
This might be an availability problem related which might be
due to the following reasons :
- The remote host is now down, either because a user turned it
off during the scan or a selected denial of service was effective against
this host
- A network outage has been experienced during the scan, and the remote
network cannot be reached from the OpenVAS server any more
- This OpenVAS server has been blacklisted by the system administrator
or by automatic intrusion detection/prevention systems which have detected the
vulnerability assessment.
In any case, the audit of the remote host might be incomplete and may need to
be done again
Details: Check open ports (OID: 1.3.6.1.4.1.25623.1.0.10919)
Version used: $Revision: 3395 $
This plugin sends packets with the 'Record Route' option. It is a complement to traceroute.
Here is the route recorded between 192.168.0.10 and 192.168.0.12 :
192.168.0.12.
Details: Record route (OID: 1.3.6.1.4.1.25623.1.0.12264)
Version used: $Revision: 3395 $
A traceroute from the scanning server to the target system was conducted. This traceroute is provided primarily for informational value only. In the vast majority of cases, it does not represent a vulnerability. However, if the displayed traceroute contains any private addresses that should not have been publicly visible, then you have an issue you need to correct.
Here is the route from 192.168.0.10 to 192.168.0.12:
192.168.0.10
192.168.0.12
Block unwanted packets from escaping your network.
Details: Traceroute (OID: 1.3.6.1.4.1.25623.1.0.51662)
Version used: $Revision: 4662 $
This routine uses information collected by other routines about CPE identities (http://cpe.mitre.org/) of operating systems, services and applications detected during the scan.
192.168.0.12|cpe:/o:microsoft:windows_xp
Details: CPE Inventory (OID: 1.3.6.1.4.1.25623.1.0.810002)
Version used: $Revision: 4482 $
Test remote host SMB Functions
OS Version = WINDOWS 5.1
Domain = VITIMAXP
SMB Serverversion = WINDOWS 2000 LAN MANAGER
Details: SMB Test (OID: 1.3.6.1.4.1.25623.1.0.90011)
Version used: $Revision: 4557 $
Detection of installed version from the NTP (Network Time Protocol) server.
This script sends request, try to get the version from the response and sets the result in KB.
Vulnerability was detected according to the Vulnerability Detection Method.
Details: NTP read variables (OID: 1.3.6.1.4.1.25623.1.0.10884)
Version used: $Revision: 4228 $
The NetBIOS port is open (UDP:137). A remote attacker may use this to gain access to sensitive information such as computer name, workgroup/domain name, currently logged on user name, etc.
The following 6 NetBIOS names have been gathered :
VITIMAXP = This is the computer name registered for workstation services by a WINS↵
client.
VITIMAXP = Computer name
GRUPO = Workgroup / Domain name
GRUPO = Workgroup / Domain name (part of the Browser elections)
GRUPO
__MSBROWSE__
The remote host has the following MAC address on its adapter :
08:00:27:3a:f3:47
If you do not want to allow everyone to find the NetBios name
of your computer, you should filter incoming traffic to this port.
Block those ports from outside communication
Details: Using NetBIOS to retrieve information from a Windows host (OID: 1.3.6.1.4.1.25623.1.0.10150)
Version used: $Revision: 3998 $
This script detects wether port 445 and 139 are open and if they are running a CIFS/SMB server.
A SMB server is running on this port
Details: SMB/CIFS Server Detection (OID: 1.3.6.1.4.1.25623.1.0.11011)
Version used: $Revision: 4261 $
It is possible to extract OS, domain and SMB server information from the Session Setup AndX Response packet which is generated during NTLM authentication.
Detected SMB workgroup: GRUPO
Detected SMB server: Windows 2000 LAN Manager
Detected OS: Windows 5.1
Details: SMB NativeLanMan (OID: 1.3.6.1.4.1.25623.1.0.102011)
Version used: $Revision: 4391 $
This script detects wether port 445 and 139 are open and if they are running a CIFS/SMB server.
A CIFS server is running on this port
Details: SMB/CIFS Server Detection (OID: 1.3.6.1.4.1.25623.1.0.11011)
Version used: $Revision: 4261 $
Checking for SMB signing is disabled.
The script logs in via smb, checks the SMB Negotiate Protocol response to confirm SMB signing is disabled.
SMB signing is disabled on this host
Details: Microsoft SMB Signing Disabled (OID: 1.3.6.1.4.1.25623.1.0.802726)
Version used: $Revision: 2576 $
Detection of Server Message Block(SMB).
This script sends SMB Negotiation request and try to get the version from the response.
Only SMBv1 is enabled on remote target
Windows 7
| Number of results: | 21 |
Port Summary
| Service (Port) | Threat Level |
| 139/tcp | Log |
| 5357/tcp | Medium |
| general/CPE-T | Log |
| general/SMBClient | Log |
| general/icmp | Log |
| 135/tcp | Medium |
| general/tcp | Low |
| 137/udp | Log |
| 445/tcp | Log |
Security Issues
Distributed Computing Environment (DCE) services running on the remote host can be enumerated by connecting on port 135 and doing the appropriate queries.
An attacker may use this fact to gain more knowledge about the remote host.
Vulnerability was detected according to the Vulnerability Detection Method.
filter incoming traffic to this port.
Details: DCE Services Enumeration (OID: 1.3.6.1.4.1.25623.1.0.10736)
Version used: $Revision: 2837 $
Distributed Computing Environment (DCE) services running on the remote host can be enumerated by connecting on port 135 and doing the appropriate queries.
An attacker may use this fact to gain more knowledge about the remote host.
Distributed Computing Environment (DCE) services running on the remote host
can be enumerated by connecting on port 135 and doing the appropriate queries.
An attacker may use this fact to gain more knowledge
about the remote host.
Here is the list of DCE services running on this host:
Port: 49152/tcp
UUID: d95afe70-a6d5-4259-822e-2c84da1ddb0d, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49152]
Port: 49153/tcp
UUID: f6beaff7-1e19-4fbb-9f8f-b89e2018337c, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49153]
Annotation: Event log TCPIP
UUID: 3c4728c5-f0ab-448b-bda1-6ce01eb0a6d5, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49153]
Annotation: DHCP Client LRPC Endpoint
UUID: 3c4728c5-f0ab-448b-bda1-6ce01eb0a6d6, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49153]
Annotation: DHCPv6 Client LRPC Endpoint
UUID: 06bba54a-be05-49f9-b0a0-30f790261023, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49153]
Annotation: Security Center
UUID: 30adc50c-5cbc-46ce-9a0e-91914789e23c, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49153]
Annotation: NRP server endpoint
Port: 49154/tcp
UUID: 86d35949-83c9-4044-b424-db363231fd0c, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49154]
UUID: a398e520-d59a-4bdd-aa7a-3c1e0303a511, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49154]
Annotation: IKE/Authip API
UUID: 552d076a-cb29-4e44-8b6a-d15e59e2c0af, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49154]
Annotation: IP Transition Configuration endpoint
UUID: 98716d03-89ac-44c7-bb8c-285824e51c4a, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49154]
Annotation: XactSrv service
UUID: 201ef99a-7fa0-444c-9399-19ba84f12a1a, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49154]
Annotation: AppInfo
UUID: 5f54ce7d-5b79-4175-8584-cb65313a0e98, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49154]
Annotation: AppInfo
UUID: fd7a0523-dc70-43dd-9b2e-9c5ed48225b1, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49154]
Annotation: AppInfo
UUID: 58e604e8-9adb-4d2e-a464-3b0683fb1480, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49154]
Annotation: AppInfo
Port: 49155/tcp
UUID: 367abb81-9844-35f1-ad32-98f038001003, version 2
Endpoint: ncacn_ip_tcp:192.168.0.13[49155]
Port: 49156/tcp
UUID: 6b5bdd1e-528c-422c-af8c-a4079be4fe48, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49156]
Annotation: Remote Fw APIs
UUID: 12345678-1234-abcd-ef00-0123456789ab, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49156]
Annotation: IPSec Policy agent endpoint
Named pipe : spoolss
Win32 service or process : spoolsv.exe
Description : Spooler service
Port: 49157/tcp
UUID: 12345778-1234-abcd-ef00-0123456789ac, version 1
Endpoint: ncacn_ip_tcp:192.168.0.13[49157]
Named pipe : lsass
Win32 service or process : lsass.exe
Description : SAM access
Solution : filter incoming traffic to this port(s).
filter incoming traffic to this port.
Details: DCE Services Enumeration (OID: 1.3.6.1.4.1.25623.1.0.10736)
Version used: $Revision: 2837 $
Xitami is prone to a denial-of-service vulnerability.
Attackers can exploit this issue to crash the affected application, denying service to legitimate users.
Xitami 5.0a0 is vulnerable.
Vulnerability was detected according to the Vulnerability Detection Method.
Details: Xitami '/AUX' Request Remote Denial Of Service Vulnerability (OID: 1.3.6.1.4.1.25623.1.0.100633)
Version used: $Revision: 3182 $
| BID: | 40027 |
| Other: | http://www.securityfocus.com/bid/40027 |
| http://www.imatix.com/products |
The remote host implements TCP timestamps and therefore allows to compute the uptime.
It was detected that the host implements RFC1323. The following timestamps were retrieved with a delay of 1 seconds in-between: Paket 1: 485537 Paket 2: 485644
A side effect of this feature is that the uptime of the remote host can sometimes be computed.
Solution type: Mitigation
To disable TCP timestamps on linux add the line 'net.ipv4.tcp_timestamps = 0' to /etc/sysctl.conf. Execute 'sysctl -p' to apply the settings at runtime.
To disable TCP timestamps on Windows execute 'netsh int tcp set global timestamps=disabled'
Starting with Windows Server 2008 and Vista, the timestamp can not be completely disabled.
The default behavior of the TCP/IP stack on this Systems is, to not use the Timestamp options when initiating TCP connections, but use them if the TCP peer that is initiating communication includes them in their synchronize (SYN) segment.
See also: http://www.microsoft.com/en-us/download/details.aspx?id=9152
TCP/IPv4 implementations that implement RFC1323.
The remote host implements TCP timestamps, as defined by RFC1323.
Special IP packets are forged and sent with a little delay in between to the target IP. The responses are searched for a timestamps. If found, the timestamps are reported.
Details: TCP timestamps (OID: 1.3.6.1.4.1.25623.1.0.80091)
Version used: $Revision: 4408 $
| Other: | http://www.ietf.org/rfc/rfc1323.txt |
The remote host responded to an ICMP timestamp request. The Timestamp Reply is an ICMP message which replies to a Timestamp message. It consists of the originating timestamp sent by the sender of the Timestamp as well as a receive timestamp and a transmit timestamp. This information could theoretically be used to exploit weak time-based random number generators in other services.
Vulnerability was detected according to the Vulnerability Detection Method.
Details: ICMP Timestamp Detection (OID: 1.3.6.1.4.1.25623.1.0.103190)
Version used: $Revision: 3115 $
| CVE: | CVE-1999-0524 |
| CERT: | CB-K15/1514 , CB-K14/0632 , DFN-CERT-2014-0658 |
| Other: | http://www.ietf.org/rfc/rfc0792.txt |
This script consolidates the OS information detected by several NVTs and tries to find the best matching OS.
Best matching OS: cpe:/o:microsoft:windows Found by NVT 1.3.6.1.4.1.25623.1.0.102011 (SMB NativeLanMan) Other OS detections (in order of reliability): OS: cpe:/o:microsoft:windows found by NVT 1.3.6.1.4.1.25623.1.0.111067 (HTTP OS Identifica↵ tion) OS: cpe:/o:microsoft:windows_8.1 found by NVT 1.3.6.1.4.1.25623.1.0.108021 (Nmap OS Identi↵ fication (NASL wrapper)) OS: cpe:/o:microsoft:windows found by NVT 1.3.6.1.4.1.25623.1.0.102002 (ICMP based OS Fing↵ erprinting)
Details: OS Detection Consolidation (OID: 1.3.6.1.4.1.25623.1.0.105937)
Version used: $Revision: 4259 $
This plugin runs nmap to identify the remote Operating System.
Detected OS: Microsoft Windows 7 SP0 - SP1, Windows Server 2008 SP1, Windows 8, or Windows↵ 8.1 Update 1 CPE: cpe:/o:microsoft:windows_8.1 Concluded from Nmap TCP/IP fingerprinting : OS details: Microsoft Windows 7 SP0 - SP1, Windows Server 2008 SP1, Windows 8, or Windows ↵ 8.1 Update 1 OS CPE: cpe:/o:microsoft:windows_7::- cpe:/o:microsoft:windows_7::sp1 cpe:/o:microsoft:win↵ dows_server_2008::sp1 cpe:/o:microsoft:windows_8 cpe:/o:microsoft:windows_8.1
Details: Nmap OS Identification (NASL wrapper) (OID: 1.3.6.1.4.1.25623.1.0.108021)
Version used: $Revision: 4662 $
| Other: | https://nmap.org/book/man-os-detection.html |
| https://nmap.org/book/osdetect.html |
A traceroute from the scanning server to the target system was conducted. This traceroute is provided primarily for informational value only. In the vast majority of cases, it does not represent a vulnerability. However, if the displayed traceroute contains any private addresses that should not have been publicly visible, then you have an issue you need to correct.
Here is the route from 192.168.0.10 to 192.168.0.13: 192.168.0.10 192.168.0.13
Block unwanted packets from escaping your network.
Details: Traceroute (OID: 1.3.6.1.4.1.25623.1.0.51662)
Version used: $Revision: 4662 $
This routine uses information collected by other routines about CPE identities (http://cpe.mitre.org/) of operating systems, services and applications detected during the scan.
192.168.0.13|cpe:/o:microsoft:windows
Details: CPE Inventory (OID: 1.3.6.1.4.1.25623.1.0.810002)
Version used: $Revision: 4482 $
Test remote host SMB Functions
OS Version = WINDOWS 7 ULTIMATE 7601 SERVICE PACK 1 Domain = SILVIO-PC SMB Serverversion = WINDOWS 7 ULTIMATE 6.1
Details: SMB Test (OID: 1.3.6.1.4.1.25623.1.0.90011)
Version used: $Revision: 4557 $
The NetBIOS port is open (UDP:137). A remote attacker may use this to gain access to sensitive information such as computer name, workgroup/domain name, currently logged on user name, etc.
The following 6 NetBIOS names have been gathered : SILVIO-PC = This is the computer name registered for workstation services by a WINS↵ client. WORKGROUP = Workgroup / Domain name SILVIO-PC = Computer name WORKGROUP = Workgroup / Domain name (part of the Browser elections) WORKGROUP __MSBROWSE__ The remote host has the following MAC address on its adapter : 08:00:27:df:3a:72 If you do not want to allow everyone to find the NetBios name of your computer, you should filter incoming traffic to this port.
Block those ports from outside communication
Details: Using NetBIOS to retrieve information from a Windows host (OID: 1.3.6.1.4.1.25623.1.0.10150)
Version used: $Revision: 3998 $
This script detects wether port 445 and 139 are open and if they are running a CIFS/SMB server.
A SMB server is running on this port
Details: SMB/CIFS Server Detection (OID: 1.3.6.1.4.1.25623.1.0.11011)
Version used: $Revision: 4261 $
It is possible to extract OS, domain and SMB server information from the Session Setup AndX Response packet which is generated during NTLM authentication.
Detected SMB workgroup: WORKGROUP Detected SMB server: Windows 7 Ultimate 6.1 Detected OS: Windows 7 Ultimate 7601 Service Pack 1
Details: SMB NativeLanMan (OID: 1.3.6.1.4.1.25623.1.0.102011)
Version used: $Revision: 4391 $
This script detects wether port 445 and 139 are open and if they are running a CIFS/SMB server.
A CIFS server is running on this port
Details: SMB/CIFS Server Detection (OID: 1.3.6.1.4.1.25623.1.0.11011)
Version used: $Revision: 4261 $
Detection of Server Message Block(SMB).
This script sends SMB Negotiation request and try to get the version from the response.
SMBv1 and SMBv2 are enabled on remote target
Details: SMB Remote Version Detection (OID: 1.3.6.1.4.1.25623.1.0.807830)
Version used: $Revision: 4262 $
This detects the HTTP Server's type and version.
The remote web server type is : Microsoft-HTTPAPI/2.0
Configure your server to use an alternate name like 'Wintendo httpD w/Dotmatrix display' Be sure to remove common logos like apache_pb.gif. With Apache, you can set the directive 'ServerTokens Prod' to limit the information emanating from the server in its response headers.
Details: HTTP Server type and version (OID: 1.3.6.1.4.1.25623.1.0.10107)
Version used: $Revision: 3564 $
This script uses DIRB to find directories and files on web applications via brute forcing. See the preferences section for configuration options.
This are the directories/files found with brute force: http://192.168.0.13:5357/
Details: DIRB (NASL wrapper) (OID: 1.3.6.1.4.1.25623.1.0.103079)
Version used: $Revision: 4685 $
This routine attempts to guess which service is running on the remote ports. For instance, it searches for a web server which could listen on another port than 80 or 443 and makes this information available for other check routines.
A web server is running on this port
Details: Services (OID: 1.3.6.1.4.1.25623.1.0.10330)
Version used: $Revision: 3923 $
The script consolidates various information for CGI scanning.
This information is based on the following scripts / settings:
- Web mirroring / webmirror.nasl (OID: 1.3.6.1.4.1.25623.1.0.10662)
- Directory Scanner / DDI_Directory_Scanner.nasl (OID: 1.3.6.1.4.1.25623.1.0.11032)
- Various OS fingerprinting methods
- The configured 'cgi_path' within the 'Scanner Preferences' of the scan config in use
The host seems to be running on a Windows operating system. The host seems to be NOT able to host PHP scripts. The host seems to be NOT able to host ASP scripts. The following directories were used for CGI scanning: http://192.168.0.13:5357/ http://192.168.0.13:5357/cgi-bin http://192.168.0.13:5357/scripts While this is not, in and of itself, a bug, you should manually inspect these directories ↵ to ensure that they are in compliance with company security standards
Details: CGI Scanning Consolidation (OID: 1.3.6.1.4.1.25623.1.0.111038)
Version used: $Revision: 4576 $
This script performs HTTP based OS detection from the HTTP banner or default test pages.
Detected OS: Microsoft Windows CPE: cpe:/o:microsoft:windows Concluded from HTTP Server banner : Server: Microsoft-HTTPAPI/2.0
Details: HTTP OS Identification (OID: 1.3.6.1.4.1.25623.1.0.111067)
Version used: $Revision: 4479 $
This plugin uses nikto(1) to find weak CGI scripts and other known issues regarding web server security. See the preferences section for configuration options.
Here is the Nikto report: - Nikto v2.1.6 --------------------------------------------------------------------------- + Target IP: 192.168.0.13 + Target Hostname: 192.168.0.13 + Target Port: 5357 + Start Time: 2016-12-15 03:09:05 (GMT0) --------------------------------------------------------------------------- + Server: Microsoft-HTTPAPI/2.0 + The anti-clickjacking X-Frame-Options header is not present. + The X-XSS-Protection header is not defined. This header can hint to the user agent to pr↵ otect against some forms of XSS + The X-Content-Type-Options header is not set. This could allow the user agent to render ↵ the content of the site in a different fashion to the MIME type + No CGI Directories found (use '-C all' to force check all possible dirs) + 7536 requests: 0 error(s) and 3 item(s) reported on remote host + End Time: 2016-12-15 03:12:50 (GMT0) (225 seconds) --------------------------------------------------------------------------- + 1 host(s) tested
Ubuntu
| Number of results: | 4 |
Port Summary
| Service (Port) | Threat Level |
| general/CPE-T | Log |
| general/icmp | Log |
| general/tcp | Log |
Security Issues
The remote host responded to an ICMP timestamp request. The Timestamp Reply is an ICMP message which replies to a Timestamp message. It consists of the originating timestamp sent by the sender of the Timestamp as well as a receive timestamp and a transmit timestamp. This information could theoretically be used to exploit weak time-based random number generators in other services.
Vulnerability was detected according to the Vulnerability Detection Method.
Details: ICMP Timestamp Detection (OID: 1.3.6.1.4.1.25623.1.0.103190)
Version used: $Revision: 3115 $
| CVE: | CVE-1999-0524 |
| CERT: | CB-K15/1514 , CB-K14/0632 , DFN-CERT-2014-0658 |
| Other: | http://www.ietf.org/rfc/rfc0792.txt |
This script consolidates the OS information detected by several NVTs and tries to find the best matching OS.
Best matching OS: cpe:/o:linux:kernel Found by NVT 1.3.6.1.4.1.25623.1.0.102002 (ICMP based OS Fingerprinting)
Details: OS Detection Consolidation (OID: 1.3.6.1.4.1.25623.1.0.105937)
Version used: $Revision: 4259 $
This plugin sends packets with the 'Record Route' option. It is a complement to traceroute.
Here is the route recorded between 192.168.0.10 and 192.168.0.11 : 192.168.0.11. 192.168.0.11.
Details: Record route (OID: 1.3.6.1.4.1.25623.1.0.12264)
Version used: $Revision: 3395 $
This routine uses information collected by other routines about CPE identities (http://cpe.mitre.org/) of operating systems, services and applications detected during the scan.
192.168.0.11|cpe:/o:linux:kernel